The Factory Reset Protection (FRP) feature was introduced on Android with the release of Android 5.1 Lollipop, which is basically meant to protect your device and prevent unauthorized usage in case it’s lost or stolen. FRP is a useful feature present on devices running Lollipop, Marshmallow and even the latest Android N developer preview comes with it. In case you aren’t aware, know about FRP first.
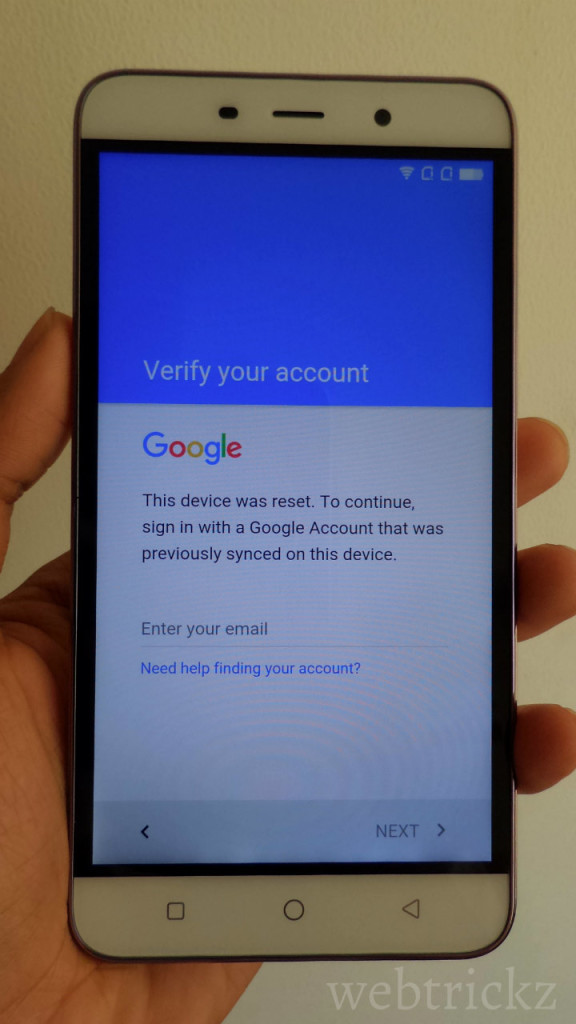
What is Factory Reset Protection (FRP)? FRP is a protection and safety feature to prevent thieves from using a stolen or lost device even if they try to hard reset the phone to factory settings or even flash it. FRP works only when you’re signed into your Google account and then if someone tries to hard reset your phone through recovery mode, they are required to enter the information for any Google account that has been earlier added to the device in order to regain access. This means the person won’t be able to use the device freely unless he enters the correct credentials. To utilize the FRP feature, one must have a Google account setup on their device and it’s recommended to use a secure screen lock so that the intruder doesn’t have the choice to factory reset the phone using the general ‘Backup and reset’ option in settings.
Being a Coolpad Note 3 user, if somehow you’ve forgot your Google account email or password and hence are stuck at Google account verification because of FRP then we’ve got you covered. I’ve figured out a simple workaround to bypass the factory reset protection on Coolpad Note 3 running Lollipop. The process should work for Coolpad Note 3 Lite as well. Watch the video tutorial below to see it in action.
This bypassing FRP trick is indeed useful but worrisome at the same time as it could potentially allow a thief to gain unauthorized access to your smartphone by following the stated steps. Considering how easily I was able to open to the locked device itself shows how poorly this function is implemented by the device manufacturer. Though, we’ve earlier seen that Google’s stock Android ROM are even vulnerable to such security issues.








how i do this in coolpad note 3 lite
sir pls help me it does not work on note 3 lite ….after erasing when i skip step after connecting 2 wifi it again starts connecting to google.. Pls help me
Right.. Same problem bro
Even after doing the steps mentioned by you in video i am not able to bypass FRP in coolpad note 3 lite. Kindly assist me on this.
Thank you
I have a Coolpad model 3622a and need past the Google account lock can someone please help me
Great thanks a lot
THIS DOESNT WORK DUDE.
GOD…..UPDATE OUR SELF DUDE
ON CURRENT NEWS AND EVENTS.
I have a cool pad catalyst and have tried every thing I had lost it a while back and it came back to me surprisingly but its not me account any more can some one plz help me